Zero Trust in OT: Micro-Segmentation That Engineers Can Maintain
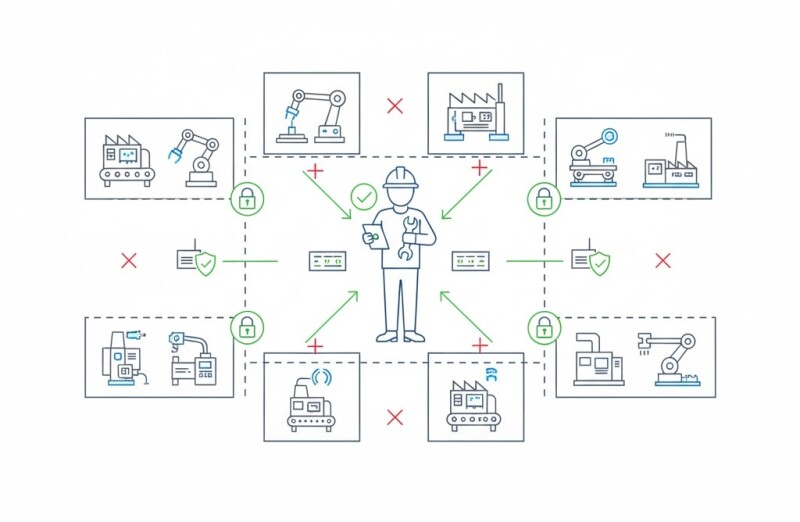
Zero Trust is reshaping how industrial networks are secured. Instead of one trusted network, every device, user, and packet must prove legitimacy. In OT, the challenge is doing this without breaking deterministic communication or adding maintenance chaos.
Why Zero Trust Matters in OT
- Legacy flat networks make lateral movement trivial after one breach.
- Remote maintenance access has expanded dramatically post-COVID.
- Regulations like NIS2 and IEC 62443 now expect segmentation by design.
Practical Micro-Segmentation
- Zones and conduits: Group PLCs, HMIs, and drives by process cell, not IP range.
- Policy enforcement: Use firewalls or SDN at conduit edges for protocol-specific rules (CIP, Modbus, OPC UA).
- Visibility: Start passive — map all traffic before enforcing anything.
Maintainability Principles
- Use templates for firewall rule creation.
- Document policies per cell — not per device.
- Automate audit exports for change control.
Example
An automotive supplier implemented Zero Trust zones using VLANs and firewall policies at the cell level. Maintenance time per rule change dropped by 60% after templating and centralized visibility.
Related Articles
- Identities for Machines: Certificates, TPMs, and Rotate at Scale
- Least Privilege for HMIs and SCADA: Design Patterns
- Measuring Zero Trust Maturity in Factories
Conclusion
Zero Trust in OT isn’t about distrust — it’s about precision. Segment once, automate maintenance, and the plant becomes resilient by default.







































Interested? Submit your enquiry using the form below:
Only available for registered users. Sign In to your account or register here.