Identities for Machines: Certificates, TPMs, and Rotate at Scale
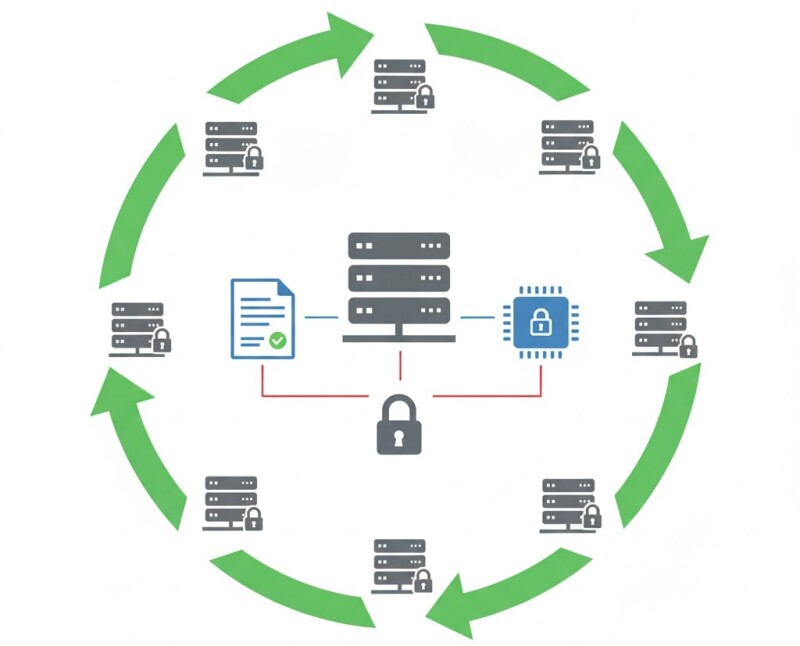
In a Zero Trust OT network, every node — from PLC to gateway — must prove its identity. Machine identities built on certificates and hardware roots of trust make that possible.
Identity Fundamentals
- X.509 Certificates: Assign unique credentials per device for mutual TLS.
- TPMs / HSMs: Securely store keys, preventing software extraction.
- Rotation: Regular renewal and revocation to avoid credential drift.
Deployment Models
- Integrate with enterprise PKI (Active Directory Certificate Services, Vault, or EJBCA).
- Use enrollment protocols (SCEP, EST) compatible with embedded controllers.
- Apply auto-rotation policies with grace periods for offline nodes.
Scalability Challenges
Plants often have thousands of devices. Automating issuance and rotation is essential. Manual certificate management becomes unfeasible beyond a few dozen nodes.
Example
A water utility rolled out TPM-backed certificates across 1,200 PLCs using EST enrollment. Full rotation completed in under 24 hours, with zero manual touchpoints.
Related Articles
- Zero Trust in OT: Micro-Segmentation That Engineers Can Maintain
- Least Privilege for HMIs and SCADA: Design Patterns
- Measuring Zero Trust Maturity in Factories
Conclusion
Certificates give machines a voice — and a fingerprint. With PKI automation and TPMs, OT systems can finally authenticate with the same rigor as IT.






































Interested? Submit your enquiry using the form below:
Only available for registered users. Sign In to your account or register here.