Coordinated Disclosure with Vendors: How to Do It Right
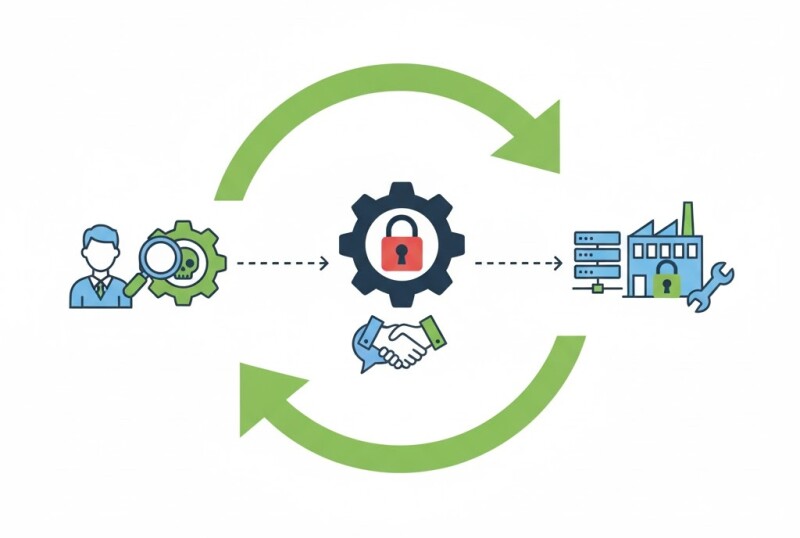
When you find a vulnerability in an industrial product, disclosure is not just an ethical duty — it’s a safety-critical process. Coordinated vulnerability disclosure (CVD) ensures issues are fixed responsibly, without exposing operational risks prematurely.
Why Coordination Matters
- Prevents exploit publication before a patch is ready.
- Gives vendors time to validate and issue firmware updates.
- Protects critical infrastructure from public zero-day exposure.
Disclosure Workflow
- Document: Reproduce the issue and record system details and proof-of-concept.
- Contact: Use the vendor’s PSIRT or CERT channel (if available).
- Negotiate: Agree on a disclosure timeline — typically 45 to 90 days.
- Coordinate: Share findings with ICS-CERT or local CSIRTs for oversight.
Communication Best Practices
- Use encrypted email or secure portals for report sharing.
- Never post exploit details online until mitigation is confirmed.
- Request CVE assignment to ensure public traceability after resolution.
Example
An automation engineer discovered hardcoded credentials in an HMI web interface. Coordinated disclosure via CISA ICS-CERT led to a patched firmware release within 60 days, credited to the finder, with no downtime in the field.
Related Articles
- SBOMs for PLCs and HMIs: What’s Realistically Possible
- Vuln Scanning without Breaking the Plant: Safe Methods
- Prioritizing Patches in OT: Risk, Windows, and Rollback
Conclusion
Responsible disclosure protects everyone — the vendor, the plant, and the ecosystem. Clear communication and agreed timelines turn vulnerabilities into resilience, not headlines.






































Interested? Submit your enquiry using the form below:
Only available for registered users. Sign In to your account or register here.