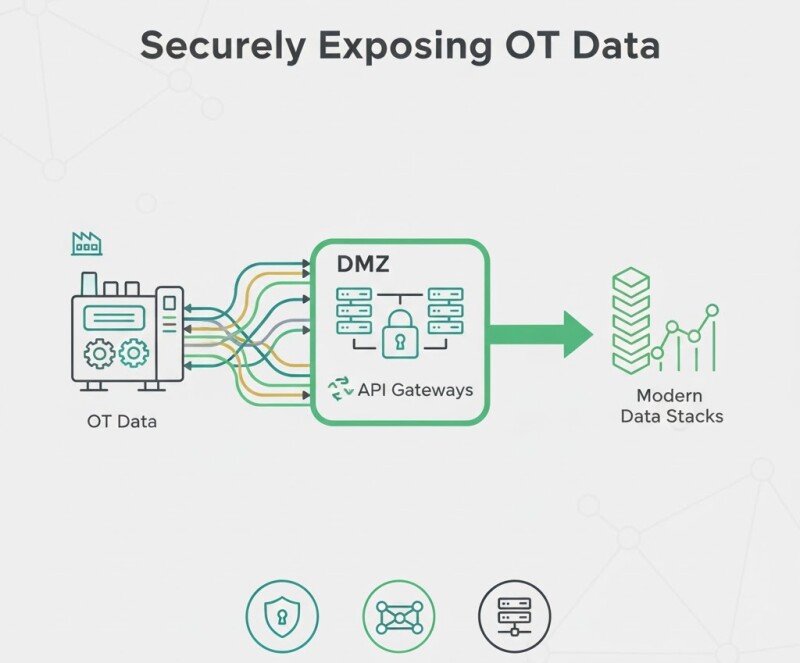
Securely Exposing OT Data: API Gateways and DMZs
Industrial data is no longer confined to the control room. But exposing it securely to IT, cloud, or partners requires a well-architected approach built on DMZ segmentation, API gateways, and least-privilege access.
1. The Role of the DMZ
A DMZ (Demilitarized Zone) isolates the plant floor from enterprise and cloud networks. Data flows one way — from OT to IT — using unidirectional gateways or brokers.
2. API Gateways for OT
- Authenticate via OAuth2 or certificates, not static keys.
- Throttle and log every call for auditability.
- Convert industrial protocols (OPC UA, MQTT) to REST or gRPC securely.
3. Security Monitoring
Integrate gateways with SIEM tools and track data egress patterns. Use anomaly detection to catch misconfigurations or data leaks early.
Example
A chemical plant built a one-way MQTT bridge through a DMZ to the corporate cloud. Result: zero direct PLC exposure and 200 ms latency for dashboard updates.
Related Articles
- Choosing an IIoT Platform in 2025: Must-Have Features
- Event-Driven Architectures in OT: MQTT, Kafka, and Pub/Sub
- Alert Fatigue in IIoT: Designing for Signal over Noise
Conclusion
Data exposure doesn’t have to mean risk. With proper DMZ design and API gateways, factories can share data safely — without opening the door to threats.







































Interested? Submit your enquiry using the form below:
Only available for registered users. Sign In to your account or register here.