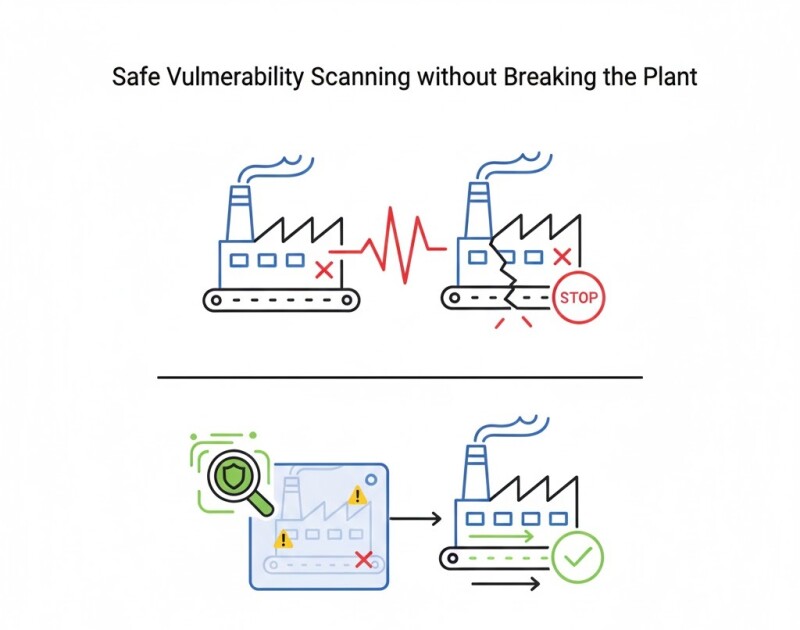
Vuln Scanning without Breaking the Plant: Safe Methods
Running traditional vulnerability scans in OT can cause communication loss, device resets, or safety trips. The goal isn’t scanning harder — it’s scanning smarter, using OT-aware methods that respect industrial constraints.
Why Standard Scanners Fail
- Send aggressive TCP probes that overload embedded stacks.
- Trigger watchdogs or safety interlocks.
- Misclassify proprietary protocols like CIP, Modbus, or PROFINET.
Safe Scanning Techniques
- Passive scanning: Monitor network traffic via SPAN ports or taps (no packets sent).
- Fingerprinting: Identify devices via banner or protocol metadata only.
- Segmented active scans: Target non-critical zones first and throttle request rate.
Tooling
- Nozomi, Claroty, and Tenable.ot provide passive discovery.
- Open tools like Zeek and Wireshark can detect CVE-related banners safely.
- Integrate with CMDB or asset management systems for automatic updates.
Case Example
A bottling facility replaced quarterly Nessus scans with passive OT inspection. Visibility increased from 65% to 94% of devices, with zero communication loss events.
Related Articles
- SBOMs for PLCs and HMIs: What’s Realistically Possible
- Prioritizing Patches in OT: Risk, Windows, and Rollback
- Asset Inventories That Stay Up-to-Date in OT
Conclusion
Scanning in OT is about precision and awareness. With passive methods and staged testing, you can maintain visibility — without risking uptime.






































Interested? Submit your enquiry using the form below:
Only available for registered users. Sign In to your account or register here.